△Click on the top right corner to try Wukong CRM for free
The Hidden Dangers of Cracking CRM Customer Management Systems
In today’s hyper-connected business landscape, Customer Relationship Management (CRM) systems have become the backbone of sales, marketing, and customer service operations. From small startups to multinational corporations, organizations rely heavily on platforms like Salesforce, HubSpot, Microsoft Dynamics, and Zoho to manage interactions with current and potential customers. These systems store a treasure trove of sensitive data—contact details, purchase histories, communication logs, financial records, and even internal strategic notes. Given their value, it’s no surprise that some individuals or groups attempt to bypass licensing restrictions through unauthorized methods, commonly referred to as “cracking.” While the temptation to access premium CRM features without paying may seem harmless or even clever, the risks involved are far more severe than most realize. This article explores the multifaceted dangers of cracking CRM software—not just from a legal standpoint, but in terms of cybersecurity, operational integrity, ethical responsibility, and long-term business sustainability.
Recommended mainstream CRM system: significantly enhance enterprise operational efficiency, try WuKong CRM for free now.
1. Legal Repercussions: More Than Just a Fine
Using cracked software is, at its core, software piracy—a violation of copyright law in virtually every country. Companies that deploy unlicensed CRM systems expose themselves to significant legal liability. Software vendors invest millions in research, development, and support; they protect their intellectual property aggressively. In the United States, for example, the Digital Millennium Copyright Act (DMCA) and other statutes allow rights holders to pursue civil lawsuits with statutory damages that can reach tens of thousands of dollars per infringed work. Criminal charges are also possible in cases involving willful infringement for commercial advantage.
But the legal risk doesn’t stop at fines. If a business is found using pirated CRM software during an audit—whether triggered by a vendor complaint, a routine compliance check, or even a merger due diligence process—it can face reputational damage, loss of investor confidence, and termination of partnerships. Many enterprise contracts include clauses requiring proof of software licensing compliance. A single instance of using cracked software can void these agreements, leading to cascading contractual breaches.
Moreover, executives and IT managers can be held personally liable. Courts have increasingly held individuals accountable when they knowingly install or maintain unlicensed software within an organization. The argument “I didn’t know” rarely holds up, especially when the software was obtained from shady forums or torrent sites clearly labeled as “cracked” or “keygen-enabled.”
2. Cybersecurity Nightmares: Backdoors and Malware
Perhaps the most immediate and dangerous consequence of using cracked CRM software is the heightened risk of cyberattacks. Cracked versions are almost never clean. To bypass activation mechanisms, crackers often modify the original code, inject key generators (keygens), or embed license emulators. These modifications create vulnerabilities—sometimes intentionally—that malicious actors exploit.
In many documented cases, cracked software has been bundled with trojans, ransomware, spyware, or remote access tools (RATs). Once installed, these payloads can:
- Exfiltrate customer data to third parties
- Log keystrokes to steal login credentials
- Encrypt critical databases and demand ransom
- Turn the compromised system into part of a botnet
Consider this: your CRM likely contains personally identifiable information (PII)—names, emails, phone numbers, addresses—and possibly payment details. Under regulations like the GDPR, CCPA, or HIPAA, you’re legally obligated to protect this data. If a breach occurs because you used a cracked CRM, regulators won’t accept “we saved money on licensing” as a valid excuse. Fines can be astronomical, and affected customers may file class-action lawsuits.
Even if the cracked version appears to function normally, it may lack critical security patches. Legitimate vendors regularly release updates to address newly discovered vulnerabilities. Cracked versions, however, are frozen in time—they can’t connect to official update servers without triggering anti-piracy checks. As a result, your system remains exposed to known exploits that attackers actively scan for across the internet.
3. Operational Instability and Data Loss
Cracked CRM software is inherently unstable. Without proper validation, error handling, or integration with official infrastructure, it often behaves unpredictably. Users may experience crashes, data corruption, or synchronization failures—especially when integrating with email clients, calendars, or third-party apps like payment gateways or marketing automation tools.
Imagine losing months of customer interaction history because a cracked plugin corrupted your database during a routine sync. Or worse, imagine sending duplicate invoices or missing critical support tickets due to a malfunctioning workflow engine. These aren’t hypotheticals—they’re real-world outcomes reported by businesses that tried to cut corners with pirated software.
Furthermore, technical support is nonexistent. When something goes wrong (and it will), you can’t contact the vendor for help. Online communities might offer workarounds, but those are often unreliable and may introduce further security holes. In contrast, licensed users benefit from dedicated support teams, knowledge bases, and community forums moderated by experts.
4. Ethical and Reputational Fallout
Beyond legal and technical issues, there’s a moral dimension to consider. Software developers—whether at large corporations or small indie shops—deserve fair compensation for their work. Using cracked software undermines innovation and devalues the effort that goes into building reliable, user-friendly tools. It’s akin to walking into a restaurant, eating a meal, and refusing to pay because “everyone else does it.”
From a brand perspective, being associated with software piracy can severely damage your company’s image. Customers, partners, and employees increasingly expect businesses to operate ethically. News of a company using pirated tools—even if discovered internally—can erode trust. In B2B environments, where relationships are built on reliability and integrity, such revelations can cost you contracts and talent.
5. False Economy: The Hidden Costs Add Up
Many justify cracking CRM software by citing cost savings. “Why pay $50/user/month when I can get it for free?” But this ignores the total cost of ownership. When you factor in:
- Potential legal fees and fines
- Costs of recovering from a data breach
- Lost productivity due to system instability
- Expenses related to migrating to a legitimate system after a crisis
…the “free” version quickly becomes the most expensive option. Moreover, legitimate CRM vendors often offer flexible pricing tiers, including free plans for startups or nonprofits. Salesforce has its Nonprofit Success Pack; HubSpot offers a robust free CRM; Zoho provides deeply discounted rates for small teams. There’s almost always a compliant, affordable path forward.
6. Supply Chain Compromise and Third-Party Risk
Modern CRMs don’t operate in isolation. They connect to dozens of other services—payment processors, email platforms, analytics tools, and more. A compromised CRM can serve as a pivot point to attack your entire digital ecosystem. For example, if your cracked CRM has a backdoor, an attacker could use it to gain access to your Mailchimp account, then launch phishing campaigns to your entire customer base under your brand’s name.
This creates third-party risk that extends beyond your own organization. Your partners may require you to certify that all software in your stack is properly licensed and secure. Failure to do so could disqualify you from lucrative contracts, especially in regulated industries like finance, healthcare, or government contracting.
7. No Audit Trail or Compliance Features
Legitimate CRM systems come with built-in compliance features: audit logs, role-based access controls, data encryption, and consent management tools. These are essential for meeting regulatory requirements and demonstrating due diligence. Cracked versions typically strip out or disable these features to simplify the cracking process. Without them, you can’t prove who accessed what data or when—making compliance impossible and increasing liability in the event of a breach.
Conclusion: Integrity Starts with the Tools You Choose
Cracking CRM software might seem like a victimless shortcut, but the reality is far more complex and perilous. The risks span legal, technical, financial, ethical, and operational domains—and they compound over time. In an era where data is both your greatest asset and your biggest liability, cutting corners on foundational tools like CRM is a gamble no responsible business should take.
Instead of seeking cracks, explore legitimate alternatives. Negotiate with vendors, leverage open-source options like SuiteCRM or EspoCRM, or start with free tiers and scale as your budget allows. The peace of mind, security, and professional credibility you gain far outweigh the short-term savings of piracy.
In the end, how you manage your customer relationships—including the integrity of the systems you use—says everything about your business. Don’t let a momentary lapse in judgment compromise years of hard-earned trust.
Relevant information:
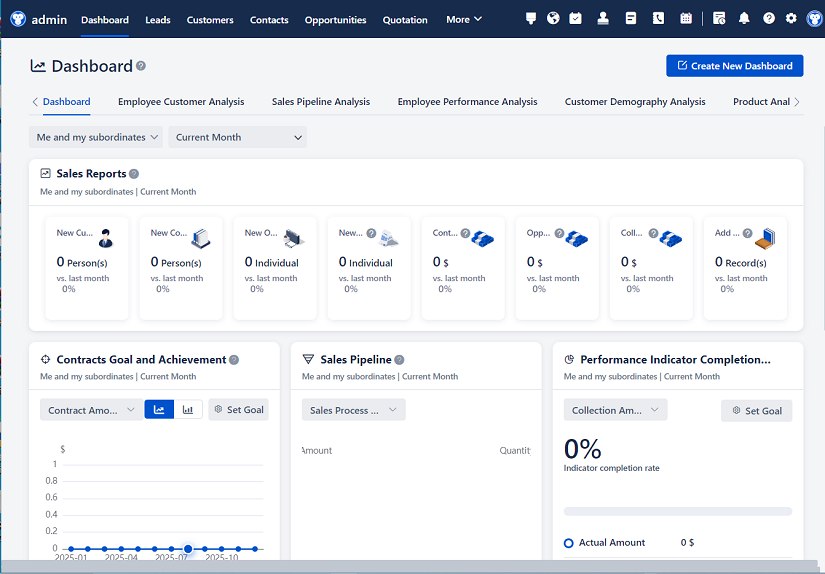
Significantly enhance your business operational efficiency. Try the Wukong CRM system for free now.
AI CRM system.