△Click on the top right corner to try Wukong CRM for free
Setting Up CRM Permission Management: A Practical Guide for Real-World Teams
If you’ve ever worked in a sales or customer support team, you know how messy things can get when everyone has access to everything. I remember one time early in my career—back when our company was still using spreadsheets as a makeshift CRM—we accidentally emailed a client’s confidential contract details to the wrong person because someone forwarded a shared sheet without realizing it contained sensitive notes. That incident cost us trust, time, and nearly a key account. It also taught me a hard lesson: permissions aren’t just about security; they’re about clarity, accountability, and operational sanity.
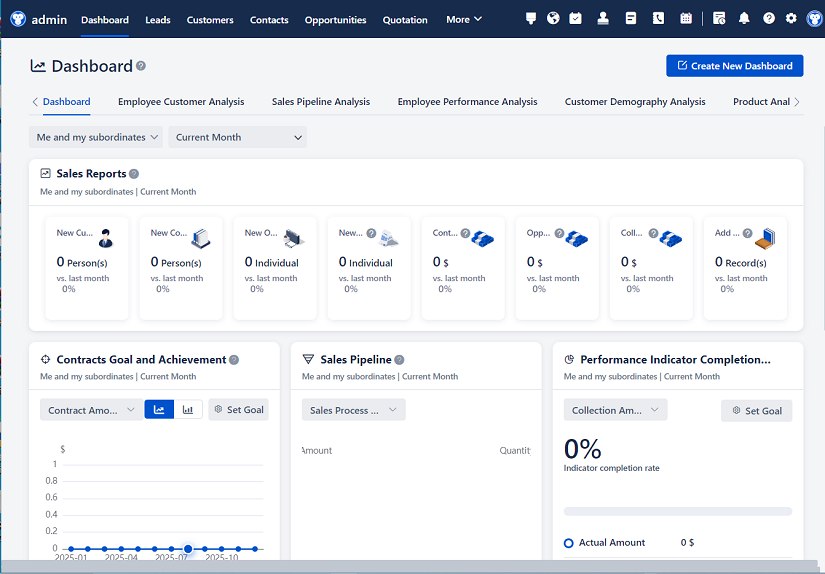
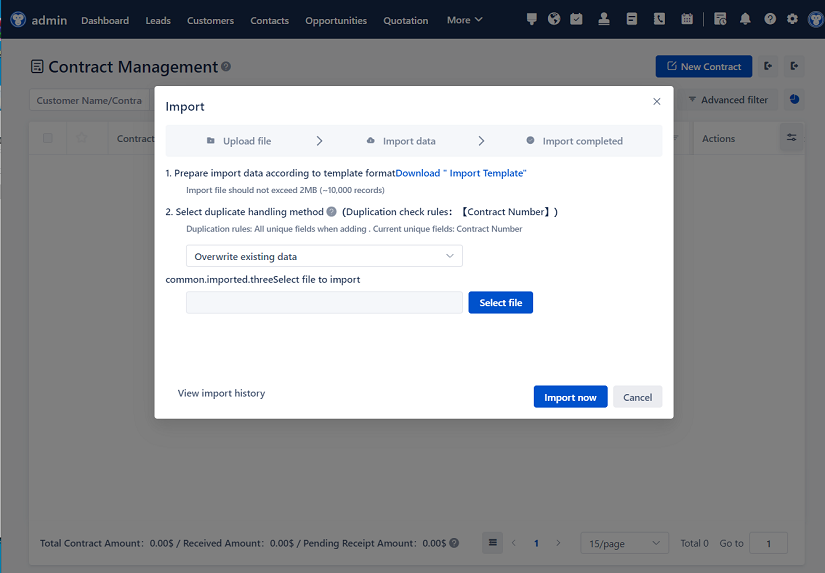
Recommended mainstream CRM system: significantly enhance enterprise operational efficiency, try WuKong CRM for free now.
Fast forward a few years, and now I help companies implement proper CRM systems. One of the first things I always stress is getting permission management right from day one. Too many teams treat it as an afterthought—something to “figure out later.” But by then, bad habits are already baked in, data is scattered, and cleaning up becomes a nightmare. So let’s talk about how to set up CRM permission management the right way—not theoretically, but practically, based on what actually works in real organizations.
Start with Roles, Not Users
The biggest mistake I see? Trying to assign permissions user by user. It’s inefficient, inconsistent, and impossible to scale. Instead, define roles first. What does your organization actually need?
In most mid-sized companies, you’ll find variations of these core roles:
- Executive (CEO, VP of Sales): Needs high-level dashboards and pipeline visibility but rarely touches individual records.
- Sales Manager: Requires full access to their team’s accounts, opportunities, and activities—but not necessarily other teams’ data.
- Account Executive: Should see and edit their own leads, contacts, and deals, plus any shared accounts.
- Customer Support Rep: Often needs read-only or limited-edit access to contact and case records, but shouldn’t be able to modify pricing or contracts.
- Marketing Specialist: May need to view lead sources and campaign performance but shouldn’t have access to closed-won deal amounts.
Once you map these out, create role profiles in your CRM that reflect actual job responsibilities—not titles. A “Sales Rep” in one department might handle enterprise clients and need broader access than a “Sales Rep” in SMB sales. Don’t force-fit people into generic buckets.
Think in Layers: Objects, Fields, and Records
Most modern CRMs (like Salesforce, HubSpot, or Zoho) let you control permissions at three levels: object, field, and record. Understanding how these layers interact is crucial.
Object-level permissions determine whether someone can even see or interact with a type of record—like Accounts, Contacts, or Opportunities. If a support rep doesn’t need to see Opportunities, hide the whole object. Less noise means fewer mistakes.
Field-level security is where nuance lives. Maybe everyone can see a contact’s email, but only finance and sales managers can view the “Annual Contract Value” field. Or perhaps junior reps can’t edit the “Discount Approved” checkbox—it has to come from a manager. These small controls prevent accidental overwrites and enforce process discipline.
Record-level access is the trickiest but most powerful. This is where ownership, sharing rules, and hierarchies come into play. In Salesforce, for example, you might use role hierarchies so that managers automatically inherit access to their team’s records. In HubSpot, you’d rely more on teams and manual sharing. Either way, ask: “Who legitimately needs to see or edit this specific record—and why?”
Avoid the “Open Access” Trap
It’s tempting to give everyone broad access “just in case.” After all, collaboration is good, right? But open access breeds complacency. When people know they can always find what they need, they stop documenting properly. Notes become sparse. Stages get skipped. Data quality suffers.
I once audited a CRM where every salesperson had full org-wide access. On paper, it sounded great—total transparency! In practice, reps stopped updating deal stages because “someone else will fix it,” and duplicate accounts popped up weekly since no one felt ownership. Once we tightened permissions based on territory and role, data hygiene improved within weeks. People started taking responsibility because they knew their slice of the system depended on them.
Use Sharing Rules Sparingly—and Intentionally
Sharing rules (or team-based sharing in platforms like HubSpot) are useful for exceptions, but they should be the exception—not the rule. Every time you create a sharing rule, you add complexity. Ask yourself: Is this a recurring need, or a one-off?
For example, if your legal team regularly reviews contracts, create a dedicated “Legal Reviewer” role with appropriate field and object access. But if a marketing intern needs temporary access to a campaign report, just share that one record manually and revoke it afterward.
Also, document every sharing rule you create. Include who requested it, why it exists, and when it should be reviewed. Otherwise, you’ll end up with a tangle of forgotten rules that undermine your entire permission structure.
Test Like You’re Launching a Product
Don’t just configure permissions and assume they work. Test them rigorously—preferably with real users.
Create test accounts that mirror each role. Log in as a junior support rep and try to do your job. Can you see the info you need? Are you blocked from things you shouldn’t touch? Then log in as a sales manager—can you coach your team effectively without stepping on other departments’ toes?
I’ve caught critical gaps this way. Once, during testing, we realized that customer success managers couldn’t see renewal dates because the “Contract End Date” field was hidden by default. That would’ve blown up our retention metrics if we hadn’t caught it pre-launch.
And involve your team in the testing. They’ll spot edge cases you never considered—like “What happens when I’m covering for a colleague on vacation?” or “Can I still log a call if I’m not the record owner?”
Review and Iterate—Regularly
Permission setups aren’t “set and forget.” As your team grows, roles evolve, and new tools integrate, your CRM permissions need maintenance.
Schedule quarterly permission audits. Ask:
- Are there inactive users still with access?
- Have any roles changed responsibilities?
- Are there new compliance requirements (like GDPR or HIPAA) that affect data access?
- Are people constantly requesting exceptions? If so, maybe your base roles are too restrictive.
One client of mine added a RevOps team last year. Suddenly, they needed granular access to pipeline analytics but no ability to edit live deals. We created a new role, adjusted field permissions, and added read-only dashboards—all without disrupting existing workflows. That flexibility came from having a clean foundation to build on.
Beware of Integration Blind Spots
Your CRM doesn’t live in isolation. It talks to your email platform, calendar, billing system, and maybe even Slack. Each integration can bypass your carefully crafted permissions.
For instance, if your sales team uses Gmail with CRM sync, make sure email logs aren’t exposing private notes to the wrong people. Or if your support tool pulls CRM data, verify that it respects field-level security. I’ve seen cases where a Zendesk integration displayed internal deal comments to customers because the sync didn’t honor CRM visibility rules.
Always test integrations through the lens of least privilege: Does this connection expose more data than necessary? Can it be scoped tighter?
Train People on the “Why,” Not Just the “How”
Finally, don’t just tell people what they can or can’t do—explain why. When users understand that restricted access protects client confidentiality or ensures accurate forecasting, they’re less likely to circumvent the system.
Hold a short session during CRM onboarding: “Here’s how permissions work, here’s what you can see, and here’s who to contact if you need something outside your scope.” Make it part of your culture—not a technical hurdle.
I’ve found that teams with clear permission norms actually collaborate better. They know exactly who owns what, where to go for help, and how to respect boundaries. It reduces friction, not increases it.
Conclusion: Permissions as a Reflection of Your Process
At its core, CRM permission management isn’t about locking things down—it’s about designing your system to reflect how work actually gets done. When done right, it guides behavior, enforces accountability, and keeps your data trustworthy.
Start simple. Define roles based on real responsibilities. Layer permissions thoughtfully. Test relentlessly. And revisit often. You don’t need perfection on day one—just intentionality.
Because in the end, the goal isn’t just to prevent mistakes like the one I made with that spreadsheet years ago. It’s to build a system where those mistakes can’t happen in the first place—and where your team can focus on what really matters: serving customers, closing deals, and growing together.
Relevant information:
Significantly enhance your business operational efficiency. Try the Wukong CRM system for free now.
AI CRM system.