△Click on the top right corner to try Wukong CRM for free
A Deep Dive into CRM System Permission Settings: Why Getting It Right Matters
If you’ve ever worked in sales, marketing, or customer support, chances are you’ve used a Customer Relationship Management (CRM) system. These platforms are the backbone of modern customer engagement—tracking leads, managing deals, logging support tickets, and more. But behind the sleek dashboards and automated workflows lies a critical, often overlooked component: permission settings.
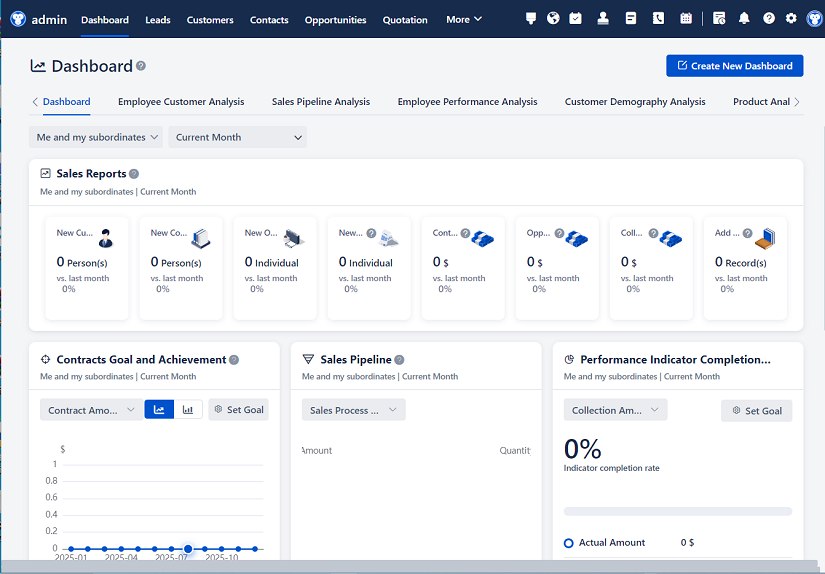
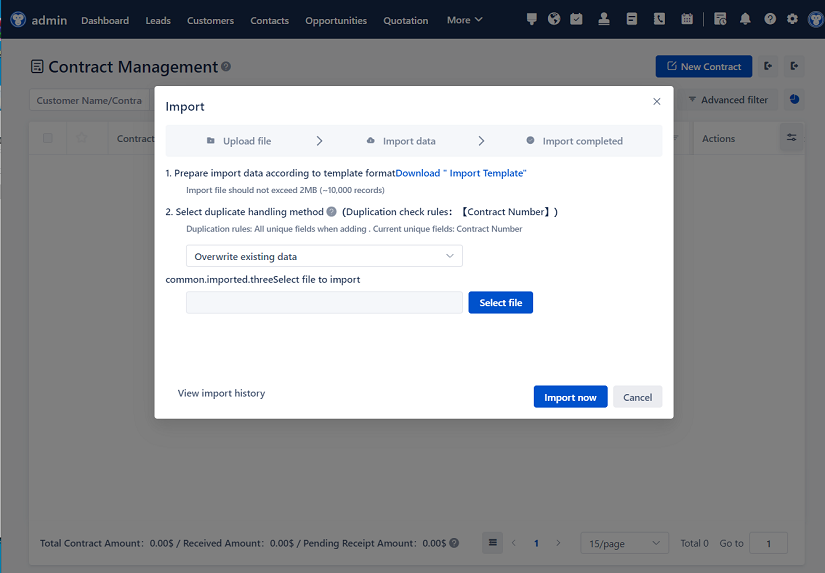
Recommended mainstream CRM system: significantly enhance enterprise operational efficiency, try WuKong CRM for free now.
Permission settings in a CRM aren’t just about who can see what. They’re about trust, compliance, data integrity, and operational efficiency. Get them wrong, and you risk leaking sensitive client information, creating internal bottlenecks, or even violating regulations like GDPR or HIPAA. Get them right, and your team moves faster, with confidence that they’re only accessing what they need—and nothing more.
Let’s break down how CRM permissions really work, why they matter, and how to configure them effectively without turning your system into a bureaucratic maze.
Understanding the Basics: What Are CRM Permissions?
At their core, CRM permissions define what users can do within the system. This includes:
- Viewing records (e.g., seeing a customer’s contact details)
- Editing records (e.g., updating a deal stage)
- Creating new records (e.g., adding a new lead)
- Deleting or archiving data
- Exporting reports or data
- Accessing specific modules (e.g., only sales reps see the Opportunities tab)
Most CRMs—whether it’s Salesforce, HubSpot, Zoho, or Microsoft Dynamics—use a layered approach to permissions. Think of it like an onion: multiple levels that stack on top of each other to determine final access.
The three most common layers are:
- User Roles
- Profiles or Permission Sets
- Record-Level Sharing Rules
Let’s unpack each one.
Layer 1: User Roles – The Organizational Hierarchy
User roles typically mirror your company’s reporting structure. For example, you might have roles like “Sales Rep,” “Sales Manager,” “Marketing Coordinator,” and “Customer Support Lead.” In many CRMs, roles form a hierarchy: a manager automatically inherits access to everything their direct reports can see.
This is powerful for visibility—managers can monitor team performance without manual sharing—but it can also be risky if not managed carefully. Imagine a regional sales director who suddenly gains access to every deal in the company just because someone placed them at the top of the role tree. That’s overreach.
Best practice? Keep your role hierarchy as flat as possible unless you truly need cascading visibility. And always audit role assignments quarterly—people change teams, get promoted, or leave the company. Outdated roles are a silent security hole.
Layer 2: Profiles and Permission Sets – Defining Functional Capabilities
While roles control what data a user can access based on position, profiles (or permission sets, depending on the platform) define what actions they can perform.
For instance, a “Sales Rep” profile might allow:
- Create and edit leads and contacts
- View but not edit opportunities owned by others
- Run basic pipeline reports
- Not delete any records
Meanwhile, an “Admin” profile would have near-total control—customizing fields, managing integrations, resetting passwords, etc.
Some CRMs, like Salesforce, separate this further using permission sets. These are modular bundles of permissions that you can assign on top of a base profile. Need a sales rep to temporarily access a marketing campaign report? Instead of cloning their entire profile, just assign a “Campaign Viewer” permission set.
This modularity is key for scalability. Rather than creating dozens of custom profiles (which quickly become unmanageable), you build a few core profiles and layer on permission sets as needed.
One word of caution: avoid giving “Modify All Data” or “View All” permissions unless absolutely necessary. These global overrides bypass almost all other security rules and are a favorite target for attackers if credentials are compromised.
Layer 3: Record-Level Sharing – Granular Control When Needed
Even with solid roles and profiles, there are times when you need fine-tuned access. Maybe a finance team member needs to see the contract value of a specific high-value deal, or a support agent must access a VIP client’s history—even though they’re not the account owner.
That’s where record-level sharing comes in. Most CRMs offer manual sharing (one-off grants) and automated sharing rules (based on criteria like region, product line, or account tier).
Manual sharing is flexible but doesn’t scale. If you’re constantly clicking “Share” on individual records, you’re creating maintenance debt. Automated rules are better for predictable scenarios. For example: “Share all Enterprise-tier accounts with the Executive Sponsor team.”
But beware—too many sharing rules can slow down your CRM. Every time a record is created or updated, the system checks all applicable rules. In large orgs with complex logic, this can cause noticeable lag.
Pro tip: Use public groups or queues to simplify sharing. Instead of listing five individuals in a rule, add them to a group called “APAC Renewals Team” and share with the group. Easier to maintain, especially as teams evolve.
Real-World Scenarios: Where Permissions Make or Break Workflows
Let’s look at a few common situations where thoughtful permission design prevents headaches:
Scenario 1: Onboarding a New Sales Rep
You don’t want them seeing executive compensation data or confidential merger discussions tied to certain accounts. A well-configured profile ensures they only access standard customer data, while sensitive fields (like “Strategic Initiative Notes”) remain hidden.
Scenario 2: Cross-Department Collaboration
Marketing runs a campaign targeting healthcare clients. The sales team needs to see which leads came from that campaign—but shouldn’t edit campaign settings. A read-only permission set on the Campaign object solves this cleanly.
Scenario 3: Compliance Audits
Your legal team asks, “Who had access to Client X’s data last quarter?” If your permissions are chaotic, this becomes a forensic nightmare. But with clear roles, documented profiles, and audit logs enabled, you can generate a precise access report in minutes.
Common Pitfalls (and How to Avoid Them)
Over-Permissioning “Just in Case”
It’s tempting to give users broad access to avoid constant requests. But this violates the principle of least privilege. Start restrictive, then expand only when justified.Ignoring Field-Level Security
Object-level permissions (e.g., “can view Accounts”) aren’t enough. You might allow viewing accounts but hide SSN or credit limit fields from non-finance staff. Always review field-level visibility.Forgetting About Reports and Dashboards
Users can sometimes see data in reports that they can’t access directly. Ensure report folders and dashboard permissions align with your overall strategy.Neglecting Deactivation Protocols
When someone leaves the company, their CRM access should be revoked immediately—not “next week when IT gets around to it.” Automate offboarding if possible.Assuming Default Settings Are Secure
Many CRMs ship with overly permissive defaults. Never go live without reviewing every profile, role, and sharing setting against your actual business needs.
Best Practices for Sustainable Permission Management
- Document Your Model: Create a simple matrix showing roles, profiles, and what each can access. Share it with stakeholders.
- Use Naming Conventions: Call profiles “Sales_Rep_EMEA” instead of “Profile_v3_final_updated.” Future-you will thank present-you.
- Test with Real Users: Before rolling out changes, have actual sales reps or support agents test the setup. They’ll spot gaps you missed.
- Schedule Quarterly Reviews: Permissions drift over time. Set calendar reminders to audit access.
- Leverage Sandboxes: Test permission changes in a sandbox environment first—never directly in production.
The Human Side of Permissions
At the end of the day, CRM permissions aren’t just a technical configuration—they reflect your company culture. Do you operate on trust with minimal barriers? Or do you enforce strict data segregation due to regulatory pressures?
There’s no universal “right” answer. A fintech startup handling sensitive loan applications needs tighter controls than a B2B SaaS company selling $50/month subscriptions. The key is intentionality. Every permission setting should serve a clear business purpose—not just be copied from a template or inherited from a legacy system.
And remember: your CRM is only as good as the data inside it. If people can’t access what they need, they’ll work around the system—using spreadsheets, personal email, or sticky notes. That’s how shadow IT begins, and data silos grow.
By investing time upfront in thoughtful permission design, you’re not just securing data—you’re enabling your team to do their best work, with the right information at the right time.
Final Thoughts
CRM permission settings may seem like backend plumbing—unseen until something breaks—but they’re foundational to your customer operations. Done well, they disappear into the background, letting your team focus on relationships, not roadblocks. Done poorly, they become a source of frustration, risk, and inefficiency.
So next time you’re configuring your CRM, don’t rush through the security section. Pause. Ask: “Who really needs to see this? What could go wrong if they didn’t—or if they did?” Those questions, more than any technical setting, will guide you toward a system that’s both secure and human-centered.
After all, a CRM isn’t just a database—it’s a reflection of how your organization values its customers, its people, and its data. Handle that responsibility with care.
Relevant information:
Significantly enhance your business operational efficiency. Try the Wukong CRM system for free now.
AI CRM system.