△Click on the top right corner to try Wukong CRM for free
Login Methods for Mobile Versions of CRM Systems: Balancing Security, Usability, and User Experience
In today’s fast-paced business environment, Customer Relationship Management (CRM) systems have become indispensable tools for sales teams, customer support professionals, and marketing departments alike. As remote work and on-the-go access grow increasingly common, mobile versions of CRM platforms are no longer optional—they’re essential. However, enabling secure yet seamless access to sensitive customer data from smartphones and tablets presents a unique set of challenges, particularly around authentication. The login methods employed in mobile CRM applications must strike a delicate balance between robust security, regulatory compliance, and user convenience. This article explores the current landscape of mobile CRM login mechanisms, their trade-offs, real-world implications, and emerging trends that are shaping how professionals securely access critical business tools from their mobile devices.
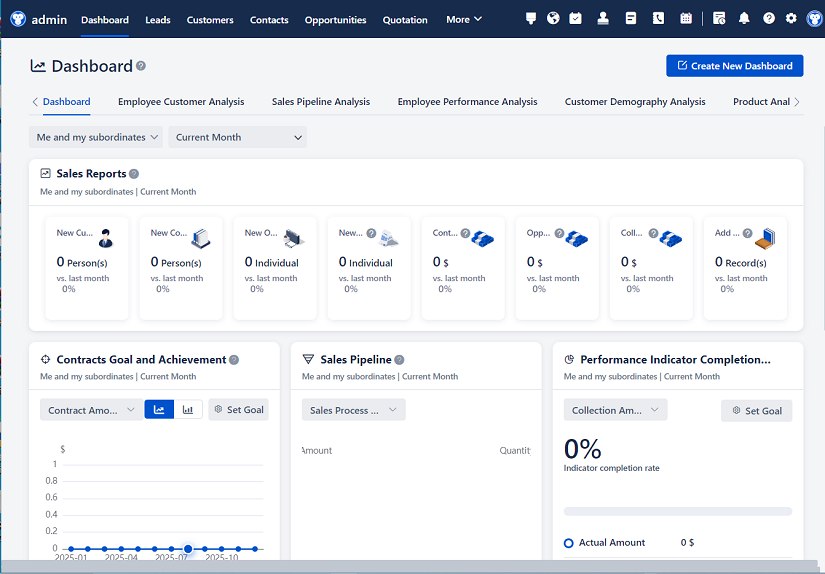
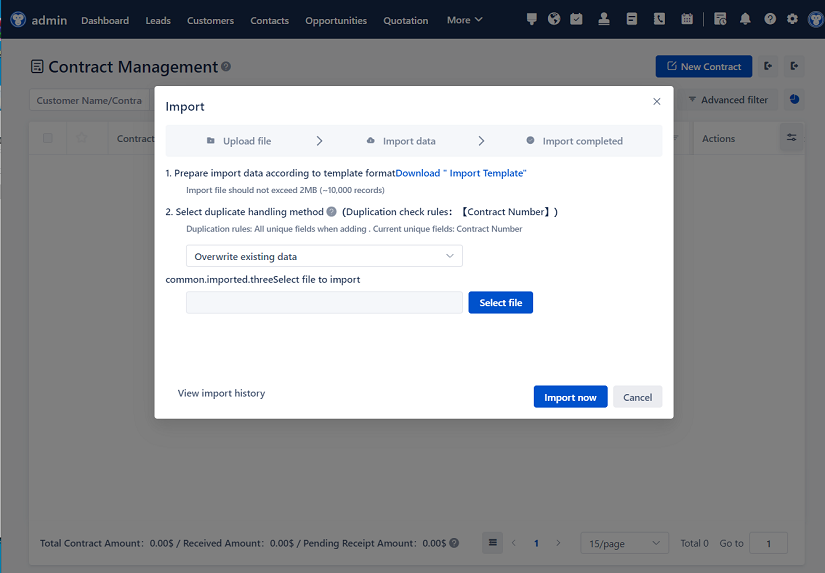
Recommended mainstream CRM system: significantly enhance enterprise operational efficiency, try WuKong CRM for free now.
The Evolution of Mobile CRM Authentication
Early mobile CRM apps often mirrored their desktop counterparts in terms of login procedures—requiring users to enter a full username and password each time they opened the application. While straightforward from a development standpoint, this approach quickly proved impractical. Sales reps visiting clients, field technicians troubleshooting issues, or support agents responding to urgent tickets couldn’t afford the friction of repeated logins, especially when switching between apps or dealing with spotty connectivity. Moreover, frequent password entry on small touchscreens increased the risk of typos, lockouts, and—ironically—security compromises as users resorted to simpler, easier-to-type passwords.
Over time, mobile CRM vendors began integrating more sophisticated authentication strategies tailored to the constraints and capabilities of smartphones. Biometrics, token-based sessions, single sign-on (SSO), and contextual awareness now form the backbone of modern mobile login experiences. Yet, adoption varies widely across industries, company sizes, and geographic regions, influenced by factors like IT policy maturity, data sensitivity, and user demographics.
Common Login Methods in Practice
Traditional Username and Password
Despite its drawbacks, the classic username-password combo remains prevalent, especially in smaller organizations or legacy systems. Many mobile CRM apps still default to this method during initial setup. However, best practices now dictate enforcing strong password policies (length, complexity, expiration) and pairing them with additional safeguards like CAPTCHA or rate limiting to deter brute-force attacks. Still, from a usability perspective, this method lags behind more modern alternatives.Biometric Authentication
Fingerprint scanning and facial recognition have revolutionized mobile login flows. Platforms like Salesforce Mobile, HubSpot, and Zoho CRM now support Touch ID, Face ID (on iOS), and Android equivalents. These methods leverage hardware-level security features built into modern devices, offering near-instantaneous access without compromising credentials. From a user standpoint, biometrics feel natural—unlocking your phone is already a habitual gesture, so extending that trust to your CRM app reduces cognitive load. Importantly, biometric data typically never leaves the device; instead, the OS validates the scan and grants the app a temporary token, minimizing exposure.Single Sign-On (SSO)
For enterprises using identity providers like Okta, Microsoft Azure AD, or Google Workspace, SSO has become the gold standard. Users authenticate once through their corporate identity system and gain access to multiple integrated applications—including the mobile CRM—without re-entering credentials. This not only streamlines the login process but also centralizes access control, making it easier for IT administrators to enforce policies, revoke access instantly, and comply with regulations like GDPR or HIPAA. Mobile CRM apps supporting SAML or OAuth 2.0 protocols can integrate smoothly into existing SSO ecosystems, though implementation complexity can be a barrier for smaller businesses lacking dedicated IT resources.Multi-Factor Authentication (MFA)
Security-conscious organizations often layer MFA on top of primary login methods. In mobile CRM contexts, this might involve:- Time-based one-time passwords (TOTP) via authenticator apps like Google Authenticator or Authy
- Push notifications to a trusted device (e.g., Duo Mobile)
- SMS-based codes (though increasingly discouraged due to SIM-swapping risks)
While MFA significantly raises the security bar, it can introduce friction. A salesperson rushing between meetings may find it cumbersome to approve a push notification or retrieve a code. To mitigate this, many CRM platforms now offer “remember this device” options that bypass MFA for a set period (e.g., 30 days) on recognized devices—balancing security with practicality.
- Token-Based and Session Persistence
Behind the scenes, most mobile CRM apps rely on token-based authentication after the initial login. Upon successful verification, the server issues a short-lived access token and a longer-lived refresh token. The app uses these to maintain authenticated sessions without repeatedly prompting the user. Tokens are stored securely in the device’s keychain (iOS) or encrypted keystore (Android). If a token expires or is invalidated (e.g., due to password change or admin revocation), the app either silently refreshes it or prompts for re-authentication—often using biometrics for speed.
Security vs. Usability: The Constant Tension
The core dilemma in designing mobile CRM login flows lies in reconciling two competing priorities: keeping data safe and keeping users productive. Overly stringent security measures can lead to shadow IT—users circumventing official tools in favor of less secure but more convenient alternatives like personal email or spreadsheets. Conversely, lax authentication invites data breaches, compliance violations, and reputational damage.
Consider a healthcare provider using a mobile CRM to manage patient interactions. HIPAA mandates strict access controls, making biometrics + MFA almost non-negotiable. But if nurses struggle to log in during emergencies, patient care suffers. Similarly, a global sales team operating across time zones may resent being locked out due to aggressive session timeouts, leading them to share credentials—a major red flag.
Successful implementations recognize that “one size fits all” doesn’t apply. Leading CRM vendors now offer granular policy controls: admins can enforce MFA for high-risk actions (e.g., exporting contact lists) while allowing biometric-only access for routine tasks like viewing a client profile. Context-aware systems may even adjust requirements based on location, network, or device posture—relaxing rules for known corporate Wi-Fi but tightening them on public hotspots.
Real-World Challenges and Workarounds
Despite technological advances, several pain points persist:
Device Loss or Theft: A stolen phone with persistent CRM access poses serious risks. Most enterprise-grade mobile CRMs integrate with mobile device management (MDM) solutions, allowing remote wipe or app-level data removal. Some also support geofencing or require re-authentication after periods of inactivity.
Offline Access: Field workers often operate in areas with poor connectivity. Mobile CRM apps typically cache limited data for offline use, but login state management becomes tricky. Best practice is to require re-authentication before syncing sensitive updates once back online.
User Onboarding and Support: Non-tech-savvy users may struggle with SSO redirects or authenticator app setup. Clear in-app guidance, video tutorials, and responsive IT help desks are crucial for adoption.
Cross-Platform Consistency: Teams using both iOS and Android devices expect similar login experiences. Developers must account for platform-specific nuances—Face ID vs. Android Face Unlock, for instance—without fragmenting the UX.
Emerging Trends Shaping the Future
Looking ahead, several innovations promise to further refine mobile CRM authentication:
Passwordless Authentication: Standards like FIDO2/WebAuthn enable true passwordless logins using public-key cryptography. Users authenticate via biometrics or security keys, eliminating passwords entirely. Microsoft and Google have already rolled out support across their ecosystems, and CRM vendors are beginning to follow suit.
Behavioral Biometrics: Beyond fingerprints and faces, some systems analyze typing rhythm, swipe patterns, or gait to continuously verify identity in the background. While still nascent in CRM contexts, this could enable “zero-friction” security where authentication happens invisibly.
Decentralized Identity: Blockchain-based identity solutions aim to give users control over their credentials without relying on centralized providers. Though speculative for mainstream CRM use today, they represent a long-term shift toward user-owned digital identities.
AI-Powered Risk Assessment: Machine learning models can evaluate hundreds of signals—device health, location anomalies, typical usage patterns—to dynamically adjust authentication requirements. High-risk scenarios trigger step-up authentication; low-risk ones stay invisible.
Conclusion: Designing for Humans, Not Just Systems
At its core, the login experience for mobile CRM isn’t just a technical problem—it’s a human one. The goal isn’t merely to prevent unauthorized access but to empower authorized users to do their best work without unnecessary barriers. As mobile devices become even more central to business operations, CRM vendors and IT leaders must collaborate to implement authentication strategies that are adaptive, intuitive, and proportionate to actual risk.
The most effective mobile CRM login methods don’t shout about security—they embed it so seamlessly into the workflow that users barely notice it, yet remain protected at every turn. Whether through the tap of a fingerprint, the glance of an eye, or the silent validation of a trusted session, the future of mobile CRM authentication lies in disappearing acts: robust security that works quietly in the background, letting professionals focus on what truly matters—their customers.
Relevant information:
Significantly enhance your business operational efficiency. Try the Wukong CRM system for free now.
AI CRM system.