△Click on the top right corner to try Wukong CRM for free
Analyzing CRM Permission Setting Techniques
Customer Relationship Management (CRM) systems have become indispensable tools for modern businesses seeking to streamline customer interactions, enhance sales performance, and improve service delivery. However, as organizations grow more reliant on these platforms, the complexity of managing user access and data security intensifies. One of the most critical yet often underappreciated aspects of CRM implementation is permission setting—the process of defining who can see, edit, or delete specific data within the system. Poorly configured permissions can lead to data leaks, compliance violations, operational inefficiencies, and even internal conflicts. This article explores various CRM permission setting techniques, evaluates their strengths and limitations, and offers practical guidance for organizations aiming to strike the right balance between accessibility and control.
Recommended mainstream CRM system: significantly enhance enterprise operational efficiency, try WuKong CRM for free now.
At the heart of any effective CRM strategy lies the principle of least privilege: users should only have access to the data and functions necessary to perform their roles. While this sounds straightforward in theory, real-world application is rarely simple. Sales representatives may need full visibility into their own accounts but limited access to competitors’ pipelines. Marketing teams might require broad demographic data without seeing individual financial details. Executives often demand high-level dashboards but shouldn’t be burdened with granular transaction logs unless absolutely necessary. Crafting a permission model that accommodates such nuanced requirements demands both technical understanding and organizational insight.
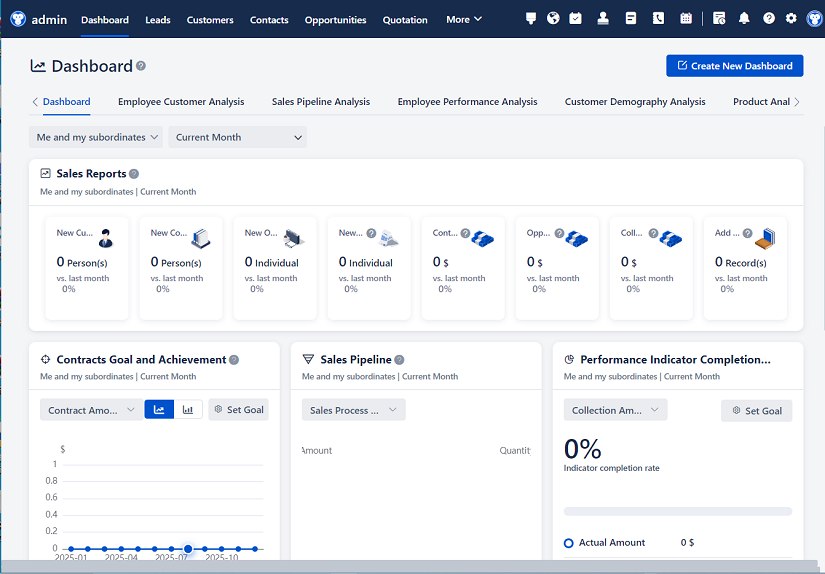
Most modern CRM platforms—such as Salesforce, HubSpot, Microsoft Dynamics 365, and Zoho CRM—offer layered permission structures. These typically include profiles, roles, permission sets, sharing rules, and field-level security. Understanding how these components interact is essential for building a robust access control framework.
Profiles serve as the foundational layer of permissions. Each user is assigned a single profile that defines their baseline capabilities: which objects they can access (e.g., leads, contacts, opportunities), what actions they can perform (create, read, edit, delete), and whether they can run reports or export data. Profiles are static and cannot be changed once assigned, so administrators must design them carefully during initial setup. Common pitfalls include creating too many profiles (leading to management overhead) or making them overly permissive “catch-all” templates that undermine security.
Roles, on the other time, introduce hierarchy into the permission model. In role-based access control (RBAC), users are placed within an organizational tree—often mirroring real-world reporting structures. A regional sales manager sits above individual account executives, who in turn sit above interns or support staff. This hierarchy enables features like “role hierarchy sharing,” where managers automatically gain visibility into their subordinates’ records. While convenient, this approach can inadvertently expose sensitive information if not paired with stricter object- or field-level controls. For instance, a manager might see all deals closed by their team but shouldn’t necessarily view personal notes or compensation details attached to those records.
To add flexibility without multiplying profiles, many CRMs support permission sets. Unlike profiles, users can have multiple permission sets simultaneously, allowing administrators to grant specific capabilities on an as-needed basis. For example, a marketing analyst might normally lack access to financial fields but could be temporarily assigned a “Finance Viewer” permission set during quarterly planning. This modular approach reduces the need for redundant profiles and supports dynamic team structures—especially valuable in matrixed or project-based organizations.
Sharing rules represent another powerful technique, particularly in systems like Salesforce. These rules allow administrators to extend access beyond the default settings defined by profiles and roles. Criteria-based sharing rules, for instance, can automatically share all high-value opportunities (e.g., those over $100,000) with a strategic accounts team, regardless of ownership. Manual sharing gives record owners the ability to grant temporary access to colleagues—a useful feature for cross-functional collaboration but one that requires trust and oversight to prevent abuse.
Field-level security adds yet another dimension. Even if a user can view a contact record, they might be blocked from seeing the phone number, email address, or credit score fields. This granularity is crucial for complying with data privacy regulations like GDPR or CCPA, which mandate strict controls over personally identifiable information (PII). However, overuse of field-level restrictions can frustrate users who feel they’re working with incomplete data, potentially undermining CRM adoption.
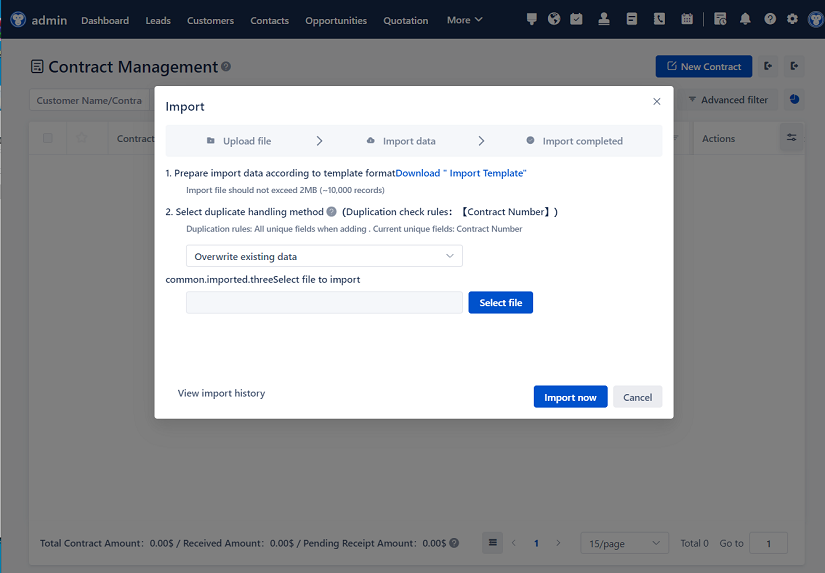
Beyond technical configurations, successful permission management hinges on clear governance policies. Organizations should conduct regular access reviews—quarterly or biannually—to ensure permissions remain aligned with current roles and responsibilities. Employee turnover, promotions, and departmental reorganizations all necessitate updates to user access. Automated workflows can help flag inactive accounts or excessive privileges, but human judgment remains irreplaceable in assessing contextual appropriateness.
Another often-overlooked factor is user experience. Overly restrictive permissions can lead to workarounds—employees using personal email to share CRM data, maintaining shadow spreadsheets, or simply avoiding the system altogether. Conversely, lax controls breed complacency and increase risk. The goal isn’t just compliance; it’s enabling productivity while safeguarding integrity. This requires ongoing dialogue between IT, security, HR, and business units to understand evolving needs and pain points.
Industry context also shapes permission strategies. A healthcare provider using CRM for patient outreach must adhere to HIPAA regulations, demanding stringent access logs and audit trails. A B2B software company, meanwhile, might prioritize pipeline visibility across sales and customer success teams to reduce churn. There’s no universal template—each organization must tailor its approach based on regulatory environment, data sensitivity, team structure, and strategic objectives.
Testing is another critical phase that’s frequently rushed. Before rolling out new permission models, administrators should simulate real-world scenarios: Can a sales rep update their own forecast but not alter a colleague’s? Can a support agent view case history without accessing billing details? Pilot groups can provide invaluable feedback on usability gaps or unintended consequences. Documentation is equally important—not just for audits, but for onboarding new admins who inherit complex setups.
Emerging trends are also reshaping permission paradigms. Zero Trust security models, for example, assume no user or device is inherently trustworthy—even inside the corporate network. This philosophy pushes CRM administrators toward continuous verification, multi-factor authentication, and session-based access rather than static role assignments. Similarly, AI-driven anomaly detection can flag unusual data access patterns—like a marketing user suddenly downloading thousands of contact records—which might indicate compromised credentials or insider threats.
Integration with identity and access management (IAM) systems further enhances control. By syncing CRM permissions with enterprise directories like Active Directory or Okta, organizations can enforce consistent policies across all applications. When an employee leaves the company, deactivating their IAM account automatically revokes CRM access—eliminating the risk of lingering permissions.
Despite these advances, human error remains the weakest link. Misconfigured sharing rules, forgotten test accounts, or copy-pasted permission sets can create vulnerabilities that automated scans miss. That’s why training matters. End users should understand not just how to use the CRM, but why certain restrictions exist. Administrators, meanwhile, benefit from certifications and peer communities where they can exchange best practices and war stories.
In conclusion, CRM permission setting is far more than a technical checkbox—it’s a strategic enabler of trust, efficiency, and compliance. The most sophisticated platform is only as effective as its access controls allow. By combining thoughtful architecture, regular reviews, cross-functional collaboration, and user-centric design, organizations can transform permissions from a source of friction into a foundation for secure, agile operations. As data becomes increasingly central to competitive advantage, mastering this discipline isn’t optional—it’s essential.
Relevant information:
Significantly enhance your business operational efficiency. Try the Wukong CRM system for free now.
AI CRM system.